
Getty Images/iStockphoto
How to create an AWS Lambda function
Many developers are turning to AWS Lambda as an alternative to EC2 instances. Here are two ways to create a Lambda function.
AWS Lambda significantly accelerates and simplifies how teams develop and maintain software. AWS Lambda eliminates the need for users to manage any servers. They can automate operational procedures, as well as complex application components. This is known as serverless infrastructure.
AWS Lambda's main resources are Lambda functions, which contain a granular piece of code that performs a specific task. To deploy a Lambda function, users upload source code and configure parameters, such as the following:
- triggers
- versions
- aliases
- memory
- permissions
- Virtual Private Cloud (VPC)
- concurrency
- destinations
- database proxies
- Elastic File System
- error handling
In this tip, we walk through how to launch Lambda functions via the AWS console and how to use AWS Serverless Application Model (SAM).
How to launch Lambda functions from the AWS console
There are many ways to launch Lambda functions. The simplest uses AWS Management Console. Developers specify the source code using the integrated development environment in the UI. From here, configure other settings, such as Identity and Access Management (IAM) permissions or environment variables.
Step 1
An easy way to create an AWS Lambda function is through the Create function button on the Lambda console. The console method suits early stages of development, rather than applications in production.

Step 2
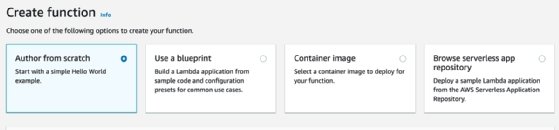
After clicking the Create function button, the next screen shows several options for the function's code. Familiarize yourself with all these options to work with Lambda functions:
- Author from scratch. Create your own code from a Hello World example.
- Use a blueprint. AWS' code blueprints include built-in AWS integrations with other services and common uses. These blueprints can save a significant amount of time when developing Lambda functions.
- Container image. Container images stored in Amazon Elastic Container Registry are also useful to launch new Lambda functions.
- Browse serverless app repository. In AWS Serverless Application Repository, users can find various helpful products.
For this example, select Author from scratch to create the function.
Step 3
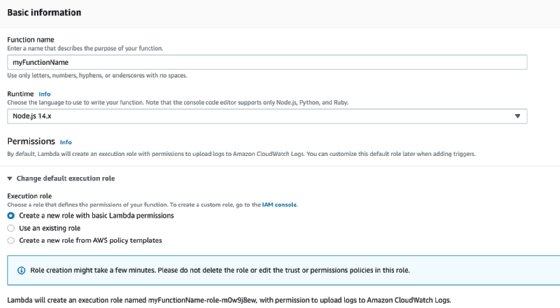
Let's proceed with a Lambda function built from scratch. The basic configuration fields include function name, runtime and permissions. Supported runtimes include programming languages such as Node.js, Go, Python, Ruby, Java, C# and .NET. Lambda also supports custom runtimes, which a developer can implement in any language that can be compiled in the Amazon Linux OS. Be aware that AWS adds new runtimes and versions to this list on an ongoing basis.
IAM roles grant permissions to Lambda functions. The default option is limited to writing data to Amazon CloudWatch logs. If a Lambda function requires permissions to call other AWS APIs, you'll need to grant enough IAM permissions for other AWS services.
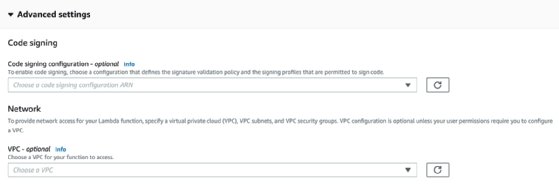
The Advanced settings section displays configurations such as code signing and VPC. Code signing adds an extra layer of security to the Lambda code. This ensures that that code hasn't been altered since a given point in time. One example is Amazon Relational Database Service instances with public access disabled.
VPC configurations enable serverless developers to deploy Lambda functions in a VPC with access to private resources. Another example is Amazon ElastiCache clusters only accessible through a VPC and DynamoDB tables with VPC endpoints enabled.
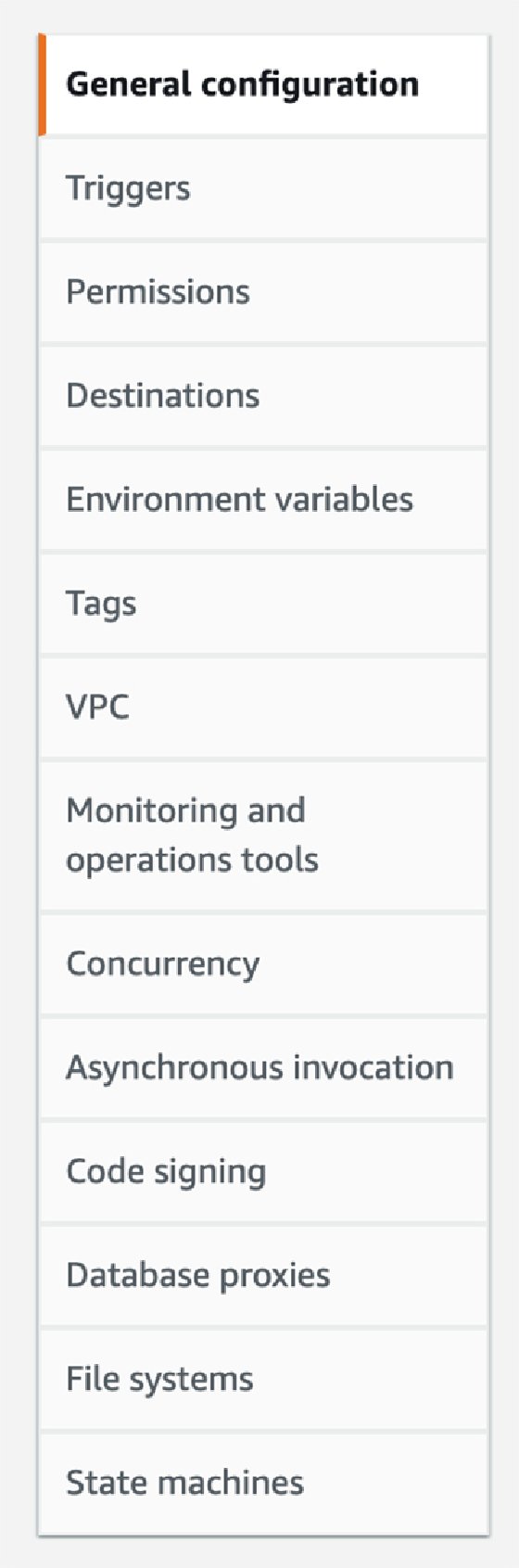
Once you create the Lambda function, add any other settings in the console. Options include triggers, environment variables and destinations as seen in Figure 5.
How to use AWS SAM
The console is a quick way to get started with functions, but it's not recommended for production-grade applications. The console doesn't provide a consistent and automated way to launch and maintain Lambda functions across different deployment stages. It also doesn't have an easy way to track code versioning and handle potential rollback scenarios.
The vendor recommends AWS SAM to deploy and maintain Lambda functions. SAM offers a mechanism to develop, test, configure and maintain functions using infrastructure as code. SAM's framework defines functions using a template in YAML format. The function tests and deployment occur via the command-line interface. This approach enables application teams to follow CI/CD best practices. The configuration parameters mentioned above can go in a SAM template.
Follow these best practices in the SAM approach:
- Group functions in one template. To deploy functions using SAM, group all functions and other relevant components, such as API gateway, REST APIs and DynamoDB tables, in the same template.
- Take advantage of native tools for automatic deployment. Automate deployment of Lambda functions using services such as AWS CodeBuild and AWS CodePipeline.
- Integrate Lambda functions. To separate code from application configuration, integrate Lambda functions with services such as AWS Secrets Manager or AWS Systems Manager Parameter Store. The developer sets up the Lambda function to fetch relevant parameters from these AWS services instead of hardcoding information into the application or enabling nonsecure access.
- Manage application-level configurations. Consider the AWS AppConfig Lambda extension to manage application-level configurations.





