
carloscastilla - Fotolia
AWS Direct Connect gateway grants your network global access
Large global enterprises will welcome AWS Direct Connect gateways, which enable multi-region connections to VPCs. However, some limitations to the service still exist.
AWS Direct Connect enables high-performance, predictable, private connections to the AWS public cloud. Many large enterprises rely on the service to facilitate connections for hybrid cloud architectures -- albeit, until recently, with one significant limitation.
A significant Direct Connect limitation had complicated life for enterprise IT teams that wished to make AWS an extension of their own IT infrastructure: A Direct Connect location could only link to a single AWS region. This forced AWS customers to jump through hoops if they wanted to spread usage across several regions for high availability and redundancy or improve performance for users in a particular global region. To do this, IT professionals either had to set up multiple Direct Connect circuits or a secondary virtual private network tunnel over the public internet.
The problem stemmed from Direct Connect's use of virtual interfaces (VIFs) that can only connect through virtual private gateways (VGWs) to an Amazon Virtual Private Cloud (VPC) or shared services within a single region. Shortly before re:Invent in 2017, Amazon unveiled Direct Connect gateways, which can help address the multi-region problem. Here's a look at some key points of the Direct Connect feature and remaining limitations.
Get familiar with gateways
An AWS Direct Connect gateway is similar to a globally distributed proxy that sits between a Direct Connect endpoint and the AWS cloud. In essence, the gateway is an amalgam of two existing Direct Connect features: VIFs and VGWs.
Any traffic that Direct Connect supports will also work with the gateway. Thus, instead of associating a Direct Connect VIF with a particular region, it connects to the gateway.
Two gateway features combine to allow multi-region connectivity. First, each customer gateway can accept connections from multiple VIFs -- Direct Connect endpoints in different locations. But the inverse is not true; you cannot associate a VIF with multiple gateways. Second, a Direct Connect gateway is a globally available resource, which means an admin can create it in any public AWS region and it can access all other public regions.
While Amazon limits VPCs to a particular region, these Direct Connect features enable gateways to allow a single VIF to connect to multiple VPCs. This, in turn, reduces the number of Border Gateway Protocol sessions between on-premises and AWS networks to improve routing efficiency.
AWS does not charge for Direct Connect gateways, but users pay hourly port charges and egress fees for data transferred out of AWS regions to Direct Connect locations; these fees adhere to standard Direct Connect prices. For example, an enterprise with data centers in the U.S. and Europe that each establish 1 Gb connections with Direct Connect endpoints and to AWS regions in the U.S., EU and Tokyo would pay the following:
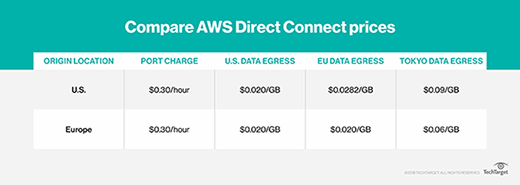
Thus, for each month, the enterprise will pay:
- $216 for each of the two Direct Connect ports, a total of $432;
- $20 per TB transferred from the U.S. region;
- $20 per TB transferred from the EU region to the European location;
- $28.20 per TB moved from the EU region to the U.S. location;
- $60 per TB transferred from the Tokyo region to Europe; and
- $90 per TB moved from the Tokyo region to the U.S. location.
Mind these limitations
Gateways improve the original Direct Connect feature set, but some restrictions remain. While these won't slow down every enterprise, IT engineers must account for these details before they implement AWS Direct Connect gateways into their enterprise networks.
First, a Direct Connect gateway, which runs under a particular AWS account, cannot connect to VPCs in another account. Don't expect this restriction to last long, as it's an issue that AWS has pledged to address.
Also, when you connect a gateway to multiple VPCs, the networks can't have overlapping IP address ranges via Classless Inter-Domain Routing blocks, because it creates routing chaos.
Gateways only support communication between Direct Connect VIFs and VPCs. In other words, you can't establish VPC-to-VPC or VIF-to-VIF connections, which effectively use the AWS backbone as a private WAN between Direct Connect locations. Gateways only allow communications between VGWs and a VIF, nothing else.
As previously mentioned, a VGW cannot associate with multiple Direct Connect gateways. Additionally, any VGW associated with a Direct Connect gateway must also be attached to a VPC.
Finally, given its general restrictions on network connectivity, Direct Connect gateways cannot connect to a VPC in the Beijing region.
Consider the alternatives
AWS users will likely find the new Direct Connect gateway the easiest way to add multi-region, native redundancy to their hybrid cloud networks. But there are plenty of other compelling options.
There are many network-as-a service providers, such as Datapath.io, Aryaka, Aviatrix and Masergy, that operate private cloud and multi-cloud backbones. These provide more options for AWS connectivity and also enable multi-cloud hybrid networks.
Before it released the Direct Connect gateway, AWS developed the Transit VPC feature as a way to enable VPC connections across regions and in multiple accounts. Transit VPC requires neither Direct Connect nor special hardware, which means any AWS customer can use it. It's comprised of a virtual Cisco Cloud Services Router -- available in the AWS Marketplace -- and various Amazon cloud services, including Lambda functions, Key Management Service and CloudFormation.
Another self-managed option on the AWS Marketplace, the SteelConnect Gateway, augments on-premises Riverbed software-defined WAN appliances with software that creates a secure network fabric between VPCs and local networks.








